“My Holo Love” is really good; this show is everything I was talking about, in my last post: augmented reality, Google glass/smart glasses, driverless cars, smart homes and the Internet of things.
Holograms marry advancements in AI, since the widespread use of digital personal assistants, like Siri and Alexa, with augmented reality, already in some video game systems, phones and virtual reality headsets.
The show is about a hologram digital personal assistant, that works through a smart glasses, that passed the Turing Test, developed by Alan Turing, in 1950. Turing helped break the German Enigma code, during WWII.
This hologram AI can also drive digitally-enhanced cars, operate smart homes and telephone land lines, and smart TVs. However, it’s not hard to see an evil version of this AI being hacked to become some kind of Skynet, HAL 9000 or Eagle Eye, that can use the power grid, power lines and the Internet of things against unsuspecting people.
Also, the AI, in the TV show, isn’t a perfect AI. It’s so human-like because it’s based on its still living creator, who lives in a lab, underscoring that there are still many things robots and AI can’t do. Other AI cultural touchstones referenced: Chobits and of course, the Spike Jonze film “Her.”
Here is what is available now – not in the near future – now: the technology to mine a nation’s cellphone network has been around for at least two decades.
In the early days of cell phone networks, agencies, such as the FBI and the NSA, perfected surveillance and data-gathering practices, that are still in use today, to police protests and track down criminals.
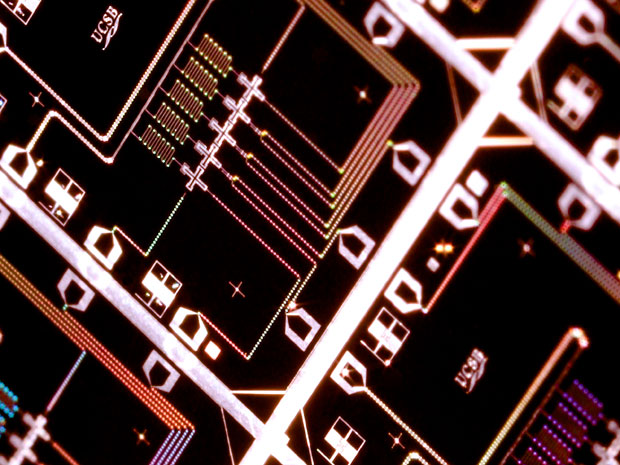
A historical tipping point was the growth of cell phone networks, in the early 2000s. The market for cell phones was mushrooming, at an exponential rate. Back then planes were developed that could log into cell phone towers, while still in the air. Every cell phone, in the midst of a call, could be scanned, and singular calls could be separated out, with accurate locations, attached to them.
An individual could carry a sensor, that could be encoded, to detect only a certain cell phone number – even if the cell phone was off. Someone could secretly power-on a phone that had already been turned off, by its owner – and then use the cell phone’s microphone, to broadcast everything and anything, in its range.
A single person can re-image several computer drives, at one time; with a fresh battery and SIM card, it is possible to clone cell phones – even without the original phone – and employ them as dummy clients, that can send and receive text messages, like the real cell phone owner.
Individuals, with pocket-sized SIM-card readers, can “borrow” a target’s phone, pull off the battery cover and copy the phone’s SIM card. The original SIM card goes back in the user’s phone – without the owner being any the wiser – while the tech-savvy operative now has the information to create dummy copies of that phone, in multiple burner phones.
As is also well-known now, cell phone calls and text messages can be monitored, for any flag-worthy information. Even back in 2003, multiple signals could be intercepted simultaneously, even as the calls and the messages were being sent out.
A group, organized enough to conduct cyber ops, can turn a national cell phone network into a gold mine of open-source intelligence. Managing the fire hose of information can be handled by gathering metadata – who, when, how long, where – on every phone call. A nifty keystroke recognition software can also secretly hack, and control a computer’s webcam or a cellphone’s camera(s), to conduct a positive-ID, of the target and his or her surrounding environment.
Cyber-defense can also be employed, to protect one’s own cell phone information, from also being siphoned off and hacked. Cordless phones can be converted into makeshift walkie-talkies – or a kit can be easily bought to build walkie-talkies, from scratch.
Other counter-measures: stop using cell phones, sometimes, to stop the data, from the phone, from being collected and used. Despite cell phone network growth, opponents can’t link a cell phone, to someone not even using a cell phone.
Internet cafes or PC rooms were – and still are – incredibly popular – but they are also mass dumping grounds for user information. Sent emails, stored on external servers, can easily be read by unfriendly eyes. Even if multiple people log in, with the same email username and password, and leave draft emails for each other – emails that are never sent, after they have yielded any useful information – an opposing force can create a warning, or a notification, whenever the same username and password is used, to log into an email account, in several locations, at the same time, or within a few hours, of each other.
Once the usernames and passwords, for target accounts, are known, an opponent can even go to an internet cafe, and upload spyware to computers, that ping every time certain usernames and passwords are used, in conjunction with one another.
Another element to avoid: opposing force operatives posing as electronics shop employees, peddling bugged cell phones and computers. Tracking down a cell phone. triangulating a phone call – pulled from real-time cell phone traffic – all of this is available and possible today, to be acquired, with ease, at a relatively low cost.

However, I want to stress that I am not a fatalist or an alarmist. I think wallowing in doomsday despair is like giving up.
There are seriously people today who believe the earth is flat, or that the moon landing was faked. The answer is not to go back, and hide in the past, or stick our heads in the sand.
I love and appreciate science, technology and medicine. There is no such thing as magic; magic, miracles and coincidences are simply science that one hasn’t understood yet.
Plus, taking the world back to the Middle Ages or the Stone Ages wouldn’t change anything. Technology and science would simply go underground, and become inaccessible to the masses again, which wouldn’t be good for humanity. Science would go back to being state secrets, coded as “magic” or “alchemy.”
Technology and science are like the devious – and righteous – nature of the human condition: it’s been around forever, and it’s here to stay, whether we like it or not. We cannot escape ourselves. The answer isn’t fear, but learning to manage these elements of our daily lives.
References
Naylor, Sean. Relentless Strike: The Secret History of Joint Special Operations Command – St. Martin’s Griffin – 2016.








You must be logged in to post a comment.